Heras UK discuss how perimeter security is an important factor in mitigating risk by deterring, delaying and detecting unwanted intrusion
Perimeter security breaches and threats are reported all too frequently in the media, creating growing concern among the UK’s businesses and critical national infrastructure. Demand for physical perimeter security is on the rise as organisations look to protect themselves against evolving cyber, criminal, terrorist threats and espionage today and in the future. In fact, the global physical security market is expected to reach USD 290.7 billion by 2025, according to a new study by Grand View Research, Inc. For businesses, critical national infrastructure, governments and even public spaces, security of premises and property, people and assets, should be a priority: it only takes one intruder in a food processing factory; one criminal breaking into a government building; one lone wolf walking into a playground… to damage a business and risk lives.
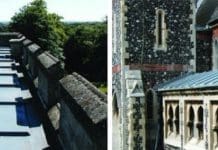
Organisations can consider a number of different ways to mitigate risk, largely depending on their own individual risk assessments. Physical perimeter protection is best explained as systems and technologies designed to protect people and assets within a defined area and often it’s the best line of defence. Technically advanced perimeter security solutions, previously used only for military facilities, critical national infrastructure and other high-risk sites, are now increasingly common both in commercial sites, public places, transport depots and many other urban and remote locations.
Deter, delay and detect
The aim should be to deter, delay and detect unwanted intrusion, while also enabling controlled access for authorised parties. Security measures can come in many forms, form of gates, bollards, fences, turnstiles which demarcate boundaries and aim to mitigate threats including vandalism, theft, and intrusion from people or even vehicles. Usually these forms of physical protection are an extremely effective deterrent, putting off criminals from launching an attack, and preventing an intrusion or damage. But, sometimes even the most secure of perimeter fences and gates experience attacks by potential intruders who will attempt to climb over or cut through to gain entry to a secure area. For such sites, it is essential to be able to reliably detect such attacks to a perimeter as early as possible.
This can be achieved through another layer of smart security in the form of Perimeter Intrusion Detection Systems (PIDS). PIDS are essentially highly specialised cables that listen for intruders and quickly notify response teams to threats by sending a secure notification via a security management system. The devices are smart enough to ignore environmental factors such as wind, rain, snow, nearby traffic, small animals and so forth, but are still able to create an alarm if there is an attempt to tamper, climb over or cut through. These systems are ideal for areas of high risk, where 24-hour circuits are needed to protect assets round the clock and can be used standalone or easily integrated into alarm systems and/or CCTV.
Physical and Smart Protection
Today, more and more organisations are choosing to combine physical protection and smart technology, as well as broader security strategies. This concept was supported recently in the Security Industry Association’s “Security Megatrends™” annual research project that reports on the top trends reshaping the security industry. It found that ‘the evolution of risk management’ would be a key megatrend for 2018. This means that the most successful management models should include all corporate stakeholders and possible sources of information to circumvent loss and reduce the potential for risk threats – instead of the traditional siloed approach. To achieve this, organisations must conduct risk assessments and understand operational requirements across the business, so that an appropriate security strategy can be developed and safeguards put in place.
Keeping ahead of potential threats is essential for organisations today. Risk of damage or loss to people, premises or data can be hugely costly, and not just in monetary terms. By understanding an organisation’s individual risk and designing security strategies around that will provide the best chance to mitigate threats or react quickly and effectively if an attack does occur.
One Heras…
Taking a holistic approach to security pays dividends and following thorough risk assessments, organisations should consider building security in layers. According to Heras, experts in perimeter protection, there are the three main building blocks: building a barrier, controlling access points, and monitoring systems to detect or prevent someone or something bypassing. Firstly, demarcation defines the boundary of a location where a protective barrier or fence should be installed. Once this has been mapped, the boundary requires secure and controlled entry points for both vehicles and pedestrians. Reliable automatic intruder detection is then needed to identify unauthorised personnel crossing a perimeter. The detection technology can integrate with an organisation’s overall security management system to ensure control room staff are notified in real time of any potential intruder.
Considerations
Key considerations for each stage of Perimeter Protection Strategy are outlined here:
Demarcate – a security perimeter should clearly show areas of ownership that should not be crossed, with visible warning signage.
Deter – a security-rated fence combined with appropriate signing offers a great deterrence. And regular inspection and maintenance is essential, because perimeters are only as secure as their weakest point. Oftentimes, it’s not needed to go beyond demarcation and deterrence – after all, the best security measures are those that never have to be fully employed. But in case they do…
Detect – when it comes to detecting suspicious behavior at the perimeter, a combination of human eyes and technology is the best solution. There are still no advanced systems that can replace the decision-making of a trained security professional, but they can significantly boost response times. There is no point implementing a measure that delays intruders for 10 minutes if the response team is 30 minutes away. Remember that electronic detection is only as good as the response it generates.
Delay – it’s essential to delay the time it takes to breach the perimeter before and after detection has taken place. No barrier or fence is impenetrable, so it’s essential to seek expert advice to match a solution to a site’s specific risks.
Controlled access – it’s vital that an organisation controls who gains access to property and who does not. Furthermore, the entrance control operator must make sure the system is safe to use. All automated gates and barriers now have stringent safety requirements.
Heras UK
Heras was founded in 1952 and has grown from a small Dutch family business specialising in fencing to an end-to-end supplier of perimeter protection solutions. Today, the company operates in over 12 countries and employs more than 1000 highly skilled experts. Heras provides well-designed, high-quality, and well-maintained perimeter protection that helps businesses meet their individual security needs. The company recently rebranded following expansion and the acquisition of key companies including Geoquip (detection), Broughton (entrance control) and Darfen (installation) in order to provide complete perimeter protection solutions and services.
Heras’s track record, combined with the ever-developing skill set of personnel enables the company to truly be experts in perimeter protection.
For more information, please visit www.heras.co.uk. Please get in touch by calling +44 161 655 1020 or emailing info@heras.co.uk.